Advanced Threat Detection And
Prevention For Trusted File Workflows
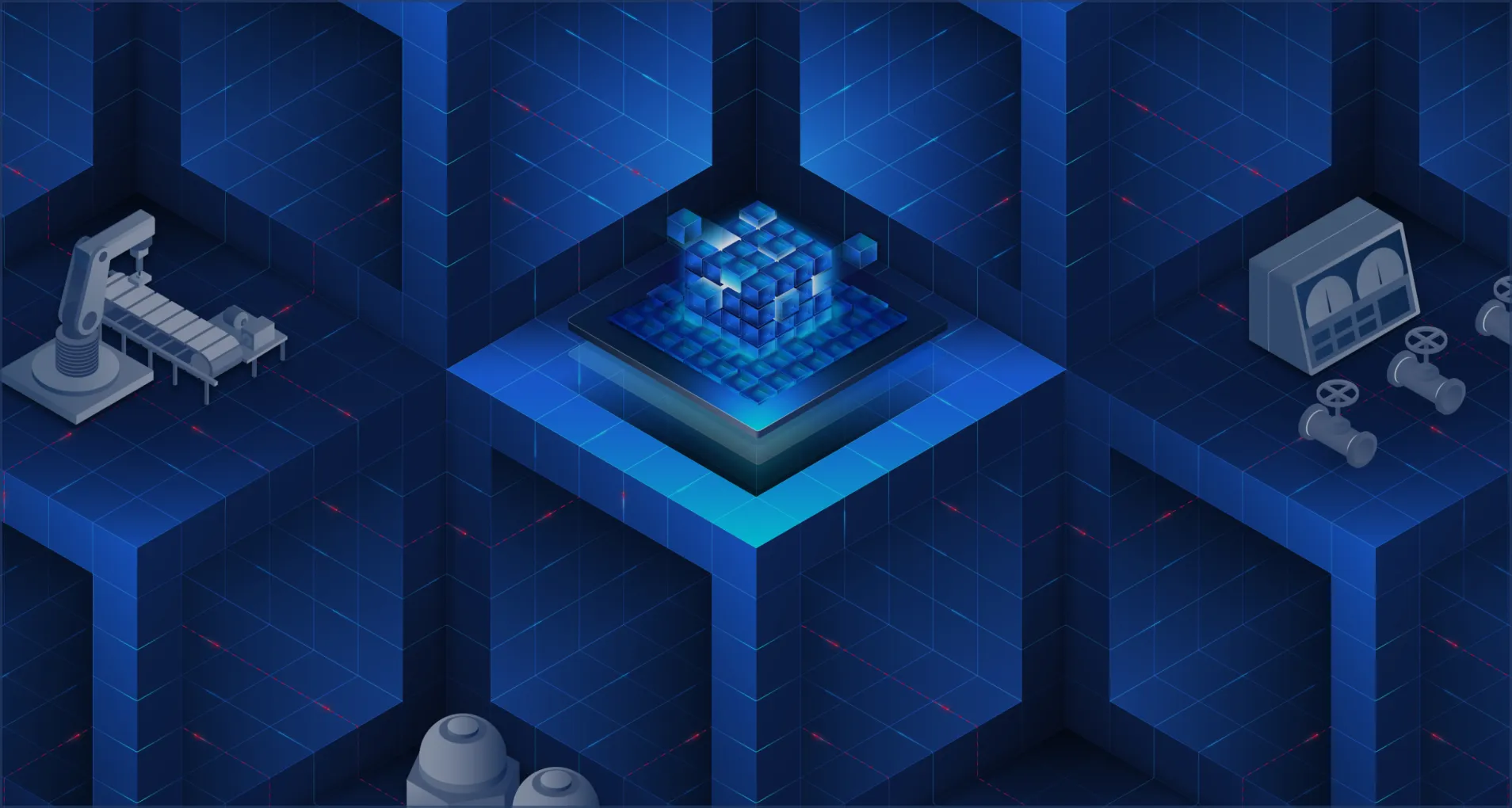
MetaDefender Core is OPSWAT’s advanced threat detection and prevention platform for identifying file-borne threats before execution. It combines Deep CDR™ Technology, Metascan™ Multiscanning, adaptive sandboxing, Proactive DLP, and AI-powered malware detection to secure file workflows across critical infrastructure while supporting compliance and zero trust at the file level.
- Turn Every File into a Trusted Asset
- Neutralize Threats Before They Proliferate
- Secure Anywhere, Scale Everywhere
OPSWAT bénéficie de la confiance de
A Platform for Complete File Trust
MetaDefender Core delivers advanced threat detection and prevention for regulated environments. Using Predictive Alin AI, Deep CDR™ Technology, Metascan™ Multiscanning, Proactive DLP™, Adaptive Sandbox Threat Intelligence, File-based Vulnerability Assessment and SBOM, it stops zero-day attacks, aids compliance, and secures every file across security workflows without slowing your business.

Detect, Analyze, and Eliminate Malware and Zero-Day Attacks
Prévention des menaces avancées
Combining industry-leading technologies like Metascan Multiscanning and Deep CDR™ Technology, MetaDefender Core detects and neutralizes embedded malware and zero-day threats.
Multi-Layered Security Architecture
A modular, policy-driven design that orchestrates scanning, sanitization, vulnerability assessment, and threat intelligence for consistent, high-volume protection across environments.
AI-Driven Threat Defense
Leveraging AI and machine learning to optimize every threat detection and prevention engine for faster, smarter, and more adaptive protection.
Centralized Policy Enforcement
Administrators can define and automate file handling policies to ensure consistent security standards across the entire organization, simplifying compliance and governance.
Seamless Integration and Scalability
Integrates easily with existing IT and OT systems through APIs, ICAP, and SDKs, adapting to complex infrastructures without disrupting operations.
Proven Protection for Regulated Environments
Trusted by governments, critical infrastructure operators, and over 2,000 global organizations, MetaDefender Core provides full control over data security while helping organizations meet regulatory requirements.
L'arrêt des menaces commence par une technologie leader sur le marché
OPSWATLa technologie éprouvée, mondialement reconnue, primée et leader sur le marché d'EMC empêche les logiciels malveillants véhiculés par les fichiers de pénétrer et de se propager dans vos environnements critiques.
Conçu pour la prédiction, l'
, conçu pour la vitesse
- Analyse approfondie de la structure des fichiers
- Modèle d'apprentissage automatique entraîné sur des menaces de type « zero-day »
Plusieurs moteurs valent mieux qu'un
- Détecter près de 100 % des logiciels malveillants
- Analyse simultanée avec plus de 30 moteurs AV de premier plan
Arrêter les menaces que les autres ne voient pas
- Prise en charge de plus de 200 formats de fichiers
- Assainissement récursif des archives imbriquées à plusieurs niveaux
- Régénérer des fichiers sûrs et utilisables
Détection du type de fichier réel pour les flux de travail critiques en matière de sécurité
- Amélioration de l'IA
- Détecte les types de fichiers falsifiés en quelques millisecondes
- Application en ligne sans perte de performances
Prévenir la perte de données sensibles
- Utiliser des modèles alimentés par l'IA pour localiser et classer les textes non structurés dans des catégories prédéfinies.
- Masquez automatiquement les informations sensibles identifiées, telles que les données à caractère personnel (PII), les informations médicales protégées (PHI) et les données relatives au secteur des cartes de paiement (PCI), dans plus de 125 types de fichiers
- Prise en charge de la reconnaissance optique de caractères (OCR) dans les images
Détecter les logiciels malveillants évasifs à l'aide d'un bac à sable avancé basé sur l'émulation
- Analyser des fichiers à grande vitesse
- Un moteur de bac à sable anti-évasion permet d'extraire les CIO
- Identifier les menaces de type "zero-day
- Classification approfondie des logiciels malveillants via l'API ou l'intégration locale
Détecter les vulnérabilités des applications avant leur installation
- Vérifier les vulnérabilités connues des logiciels avant de les installer
- Analyser les systèmes pour détecter les vulnérabilités connues lorsque les appareils sont au repos
- Examiner rapidement les applications en cours d'exécution et leurs bibliothèques pour détecter les vulnérabilités.
MetaDefender Core File Processing Workflow
Every step is designed to protect your data. Any file entering MetaDefender Core follows a controlled, multi-stage workflow designed to detect, sanitize, and verify content before it’s released into secure networks. This process ensures that even complex, nested files are fully analyzed and compliant with organizational security policies. Each stage is modular, policy-driven, and optimized for performance and accuracy across IT, OT, and air-gapped environments.

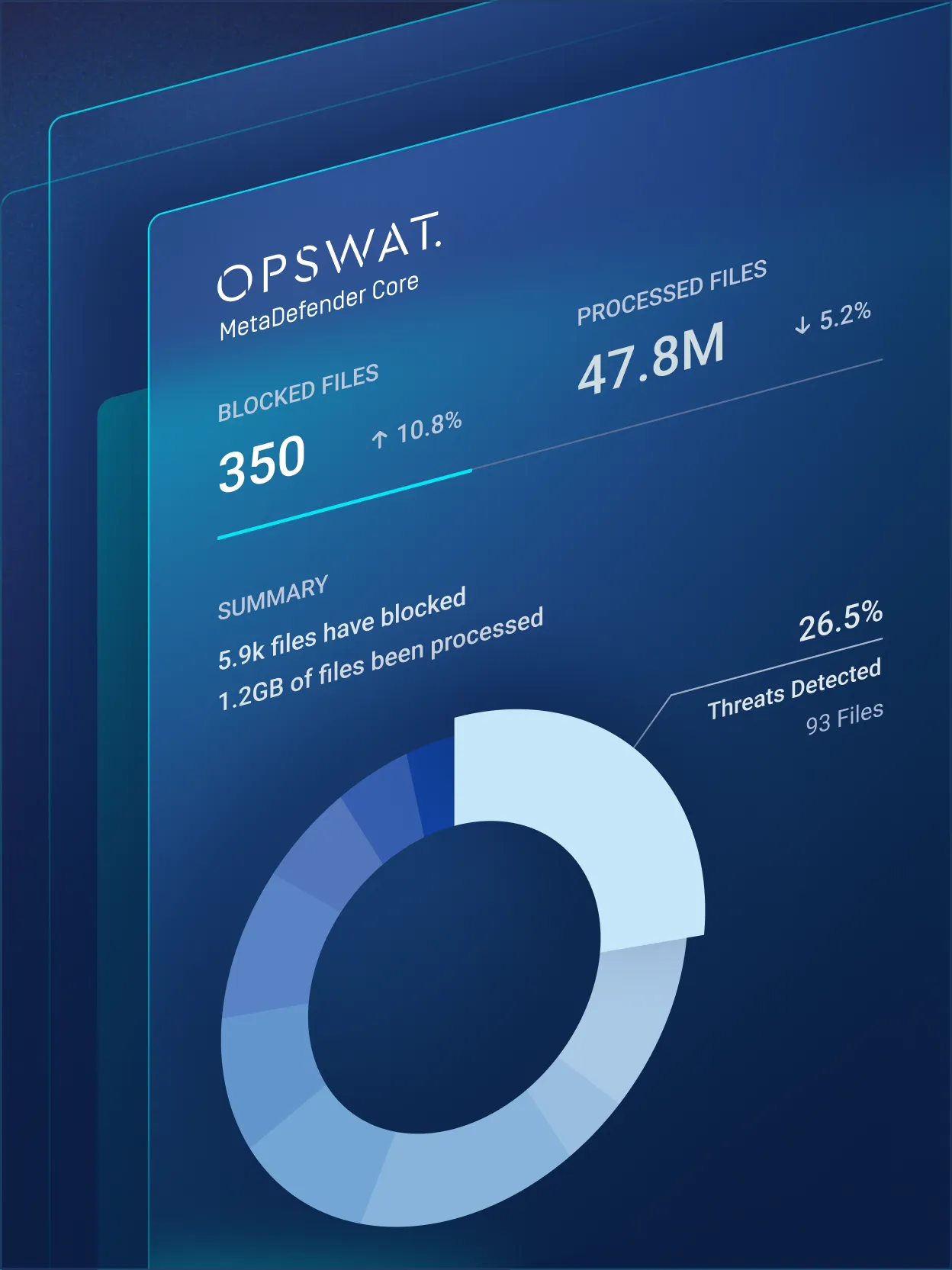
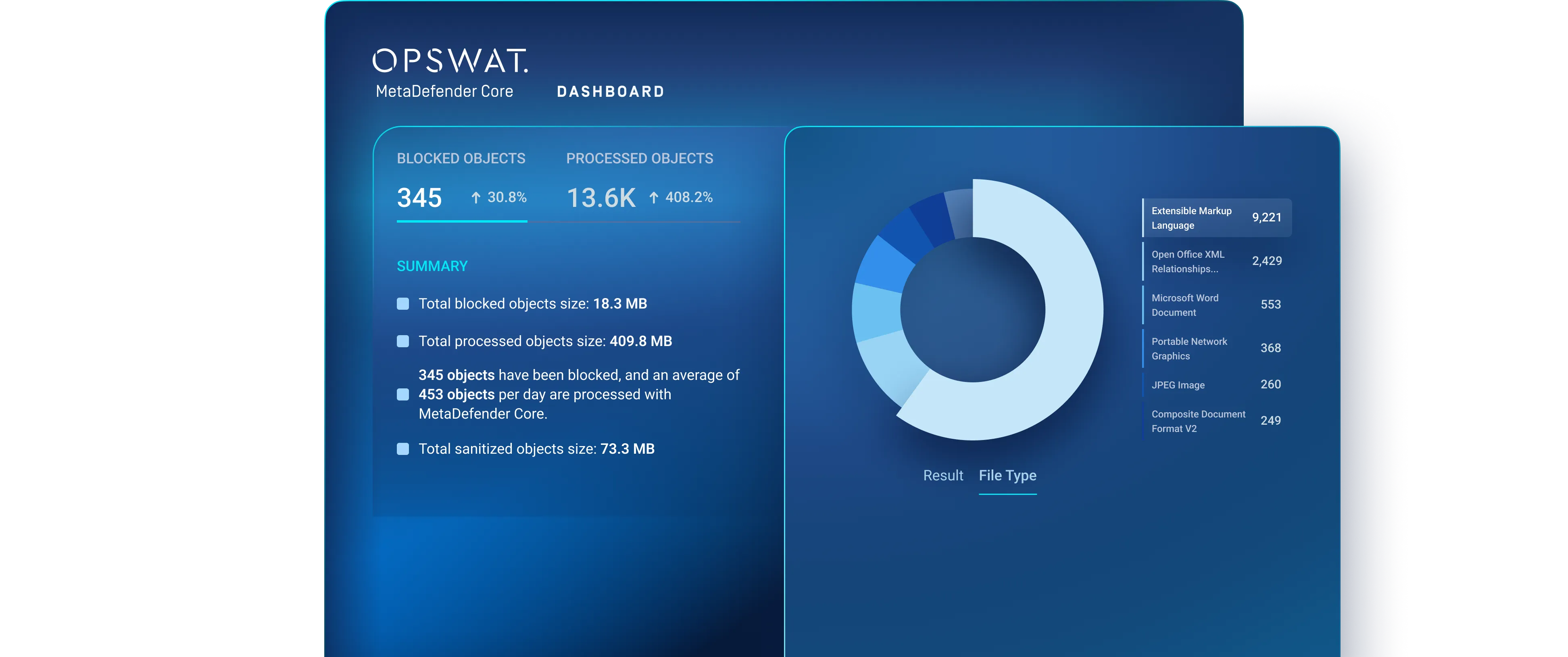
MetaDefender Core in Action
Gain complete visibility and control over file security, from detection and sanitization to verification and delivery.
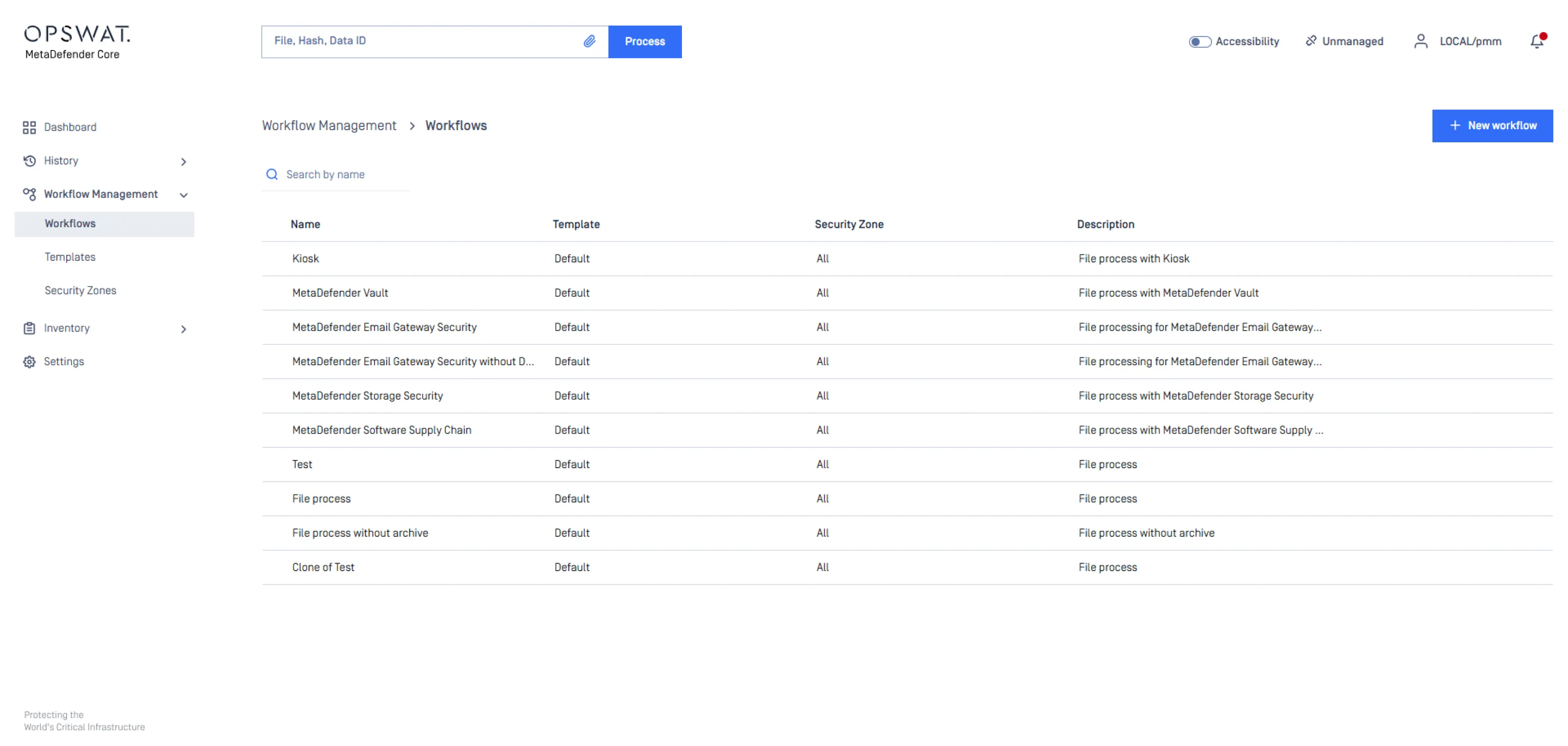
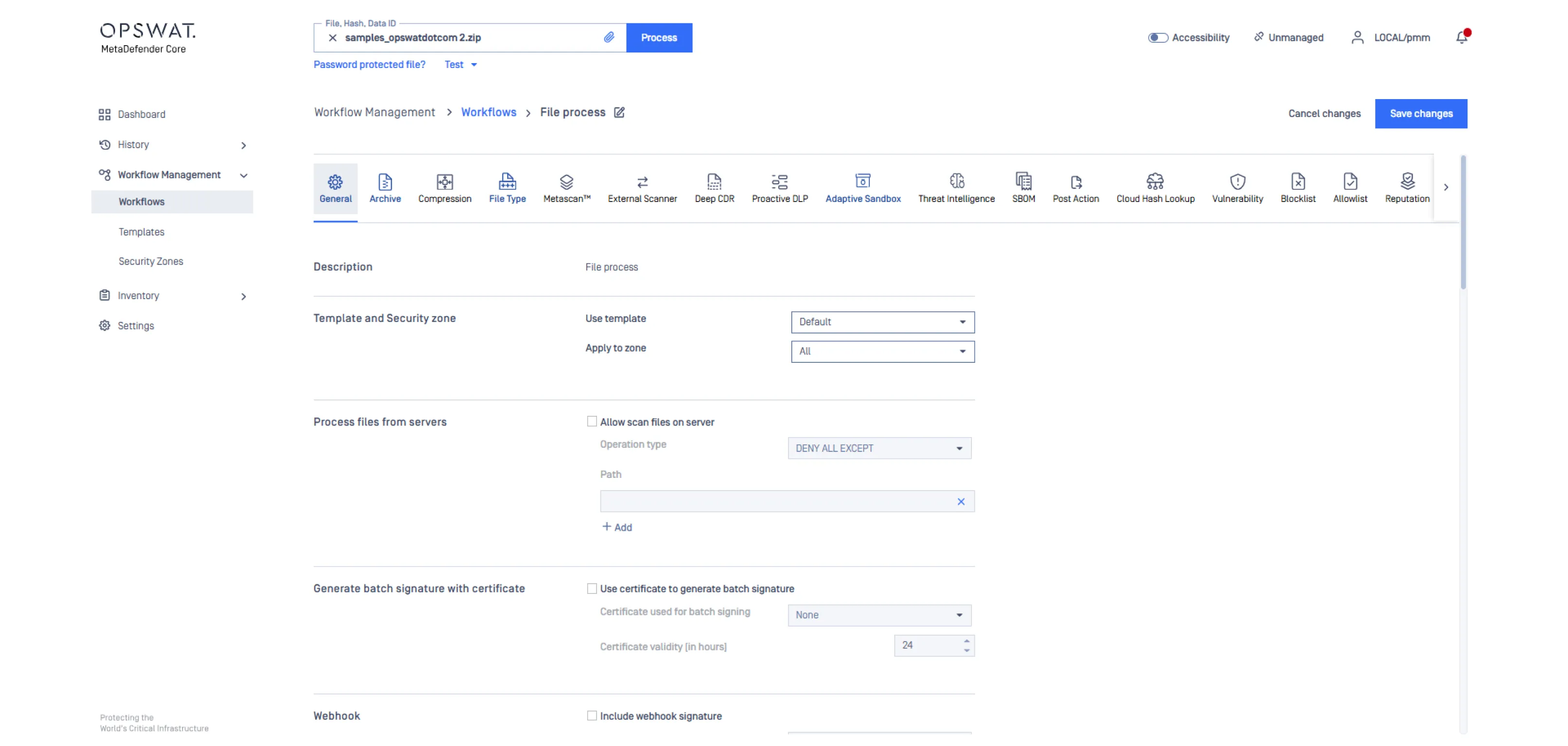
Configure security aligned workflows to match your operational policies across email, file transfer, storage, or custom environments. Establish how files enter the system and how they are processed.
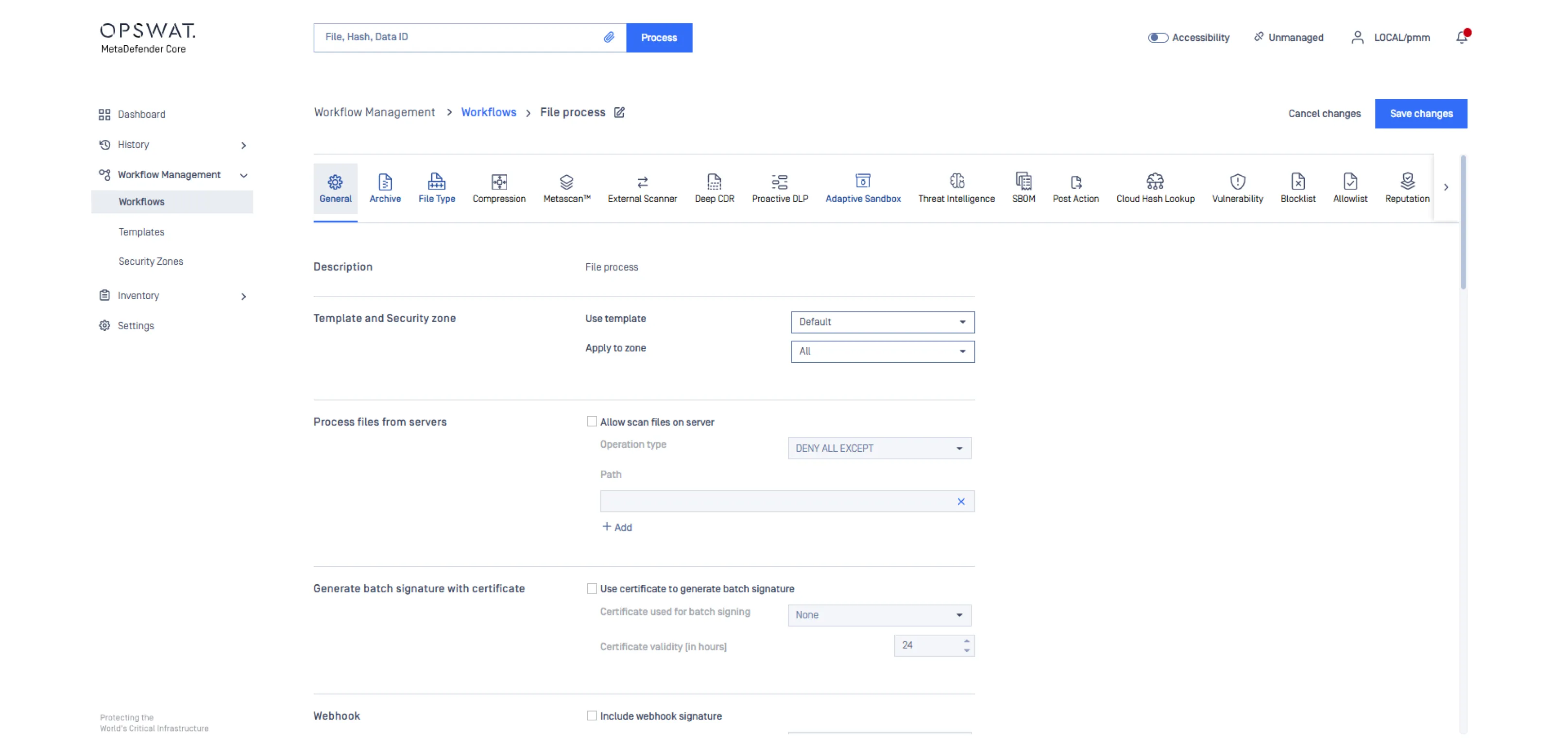
Use a modular set of layered detection and prevention engines including File Type Detection, Deep CDR™ Technology, Multiscanning, Proactive DLP, and Adaptive Sandbox. This allows you to design specific file processing flows that match your operational use cases and security requirements.
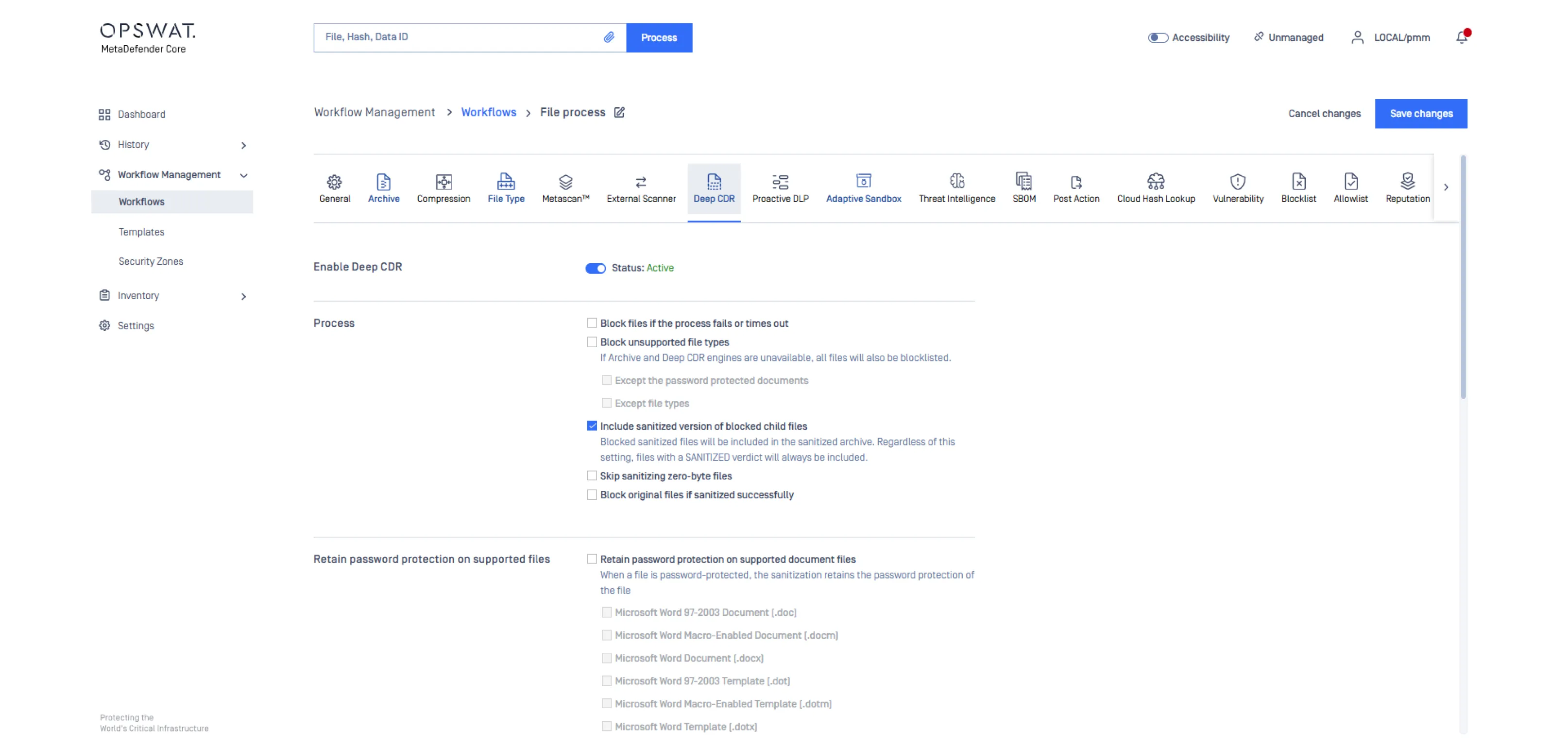
Define how files are inspected and cleaned through strict file type detection, recursive archive extraction, and Deep CDR™ Technology policies. Configure rules that govern how content is analyzed, reconstructed, and approved before it is released to downstream systems.
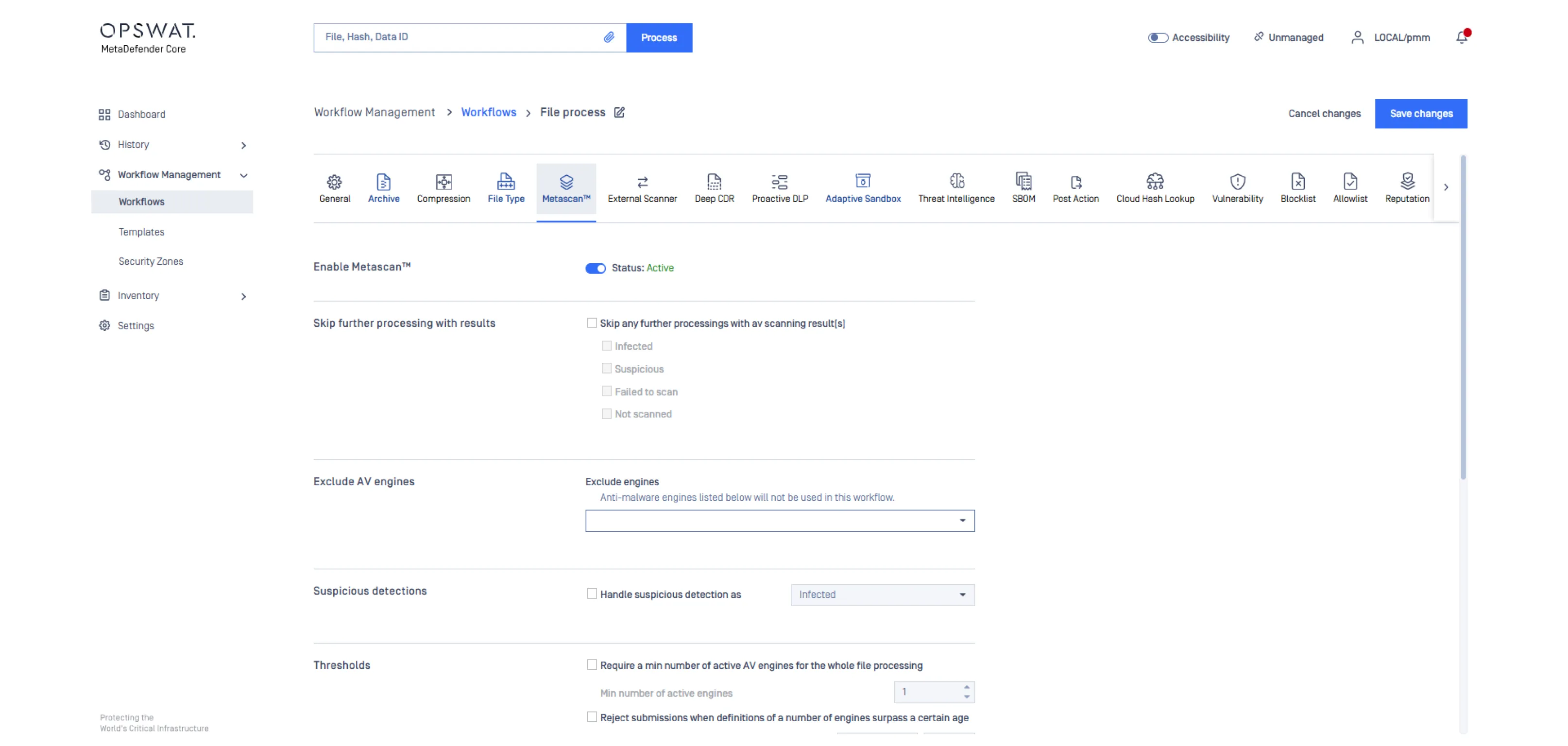
Configure antivirus engines based on the package you have licensed and tailor how they contribute to threat evaluation. Adjust detection scoring, engine selection, scanning depth, and performance settings to achieve balanced and comprehensive threat coverage.
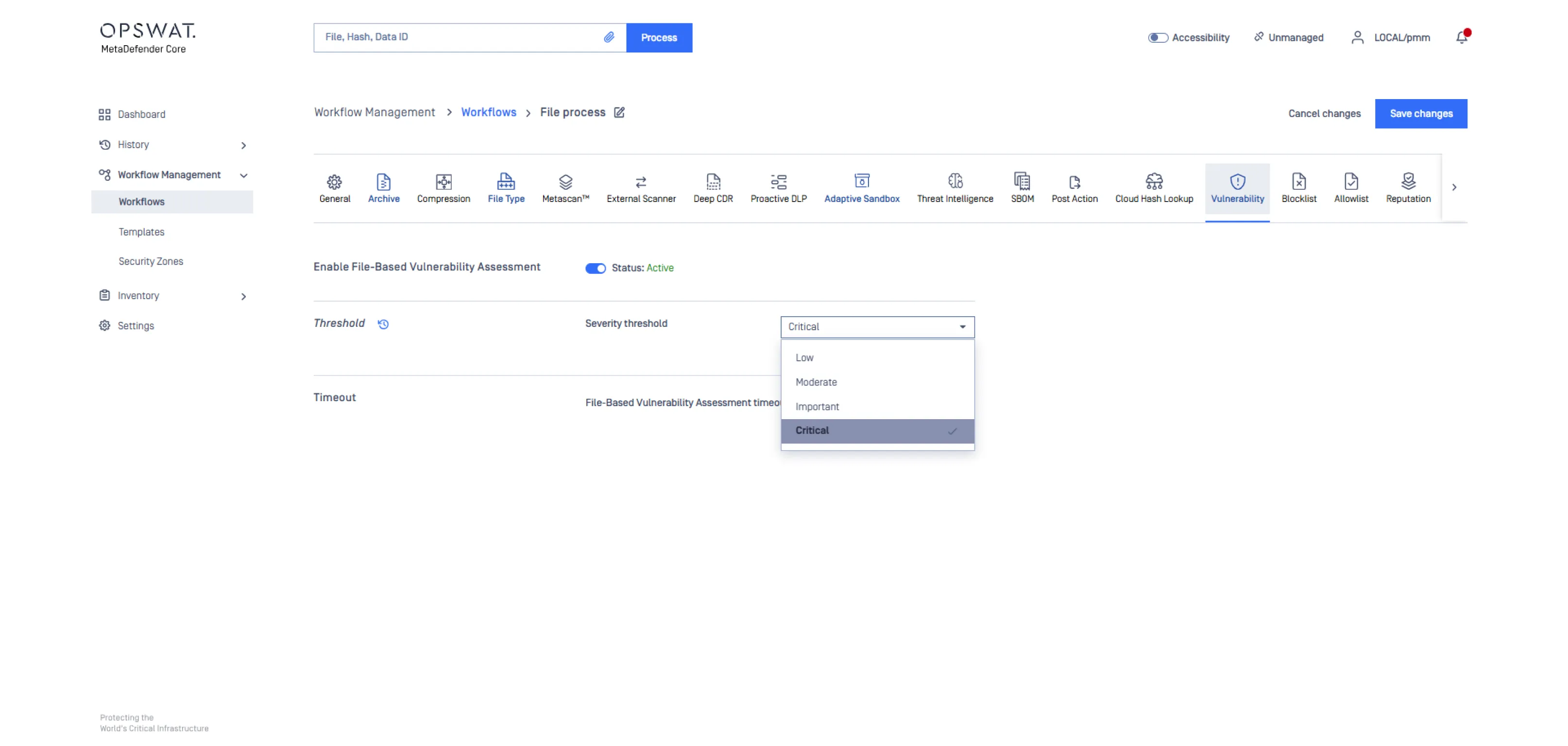
Enable vulnerability analysis for files, installers, and executables. Set rules to detect outdated libraries and known vulnerabilities before allowing file usage.
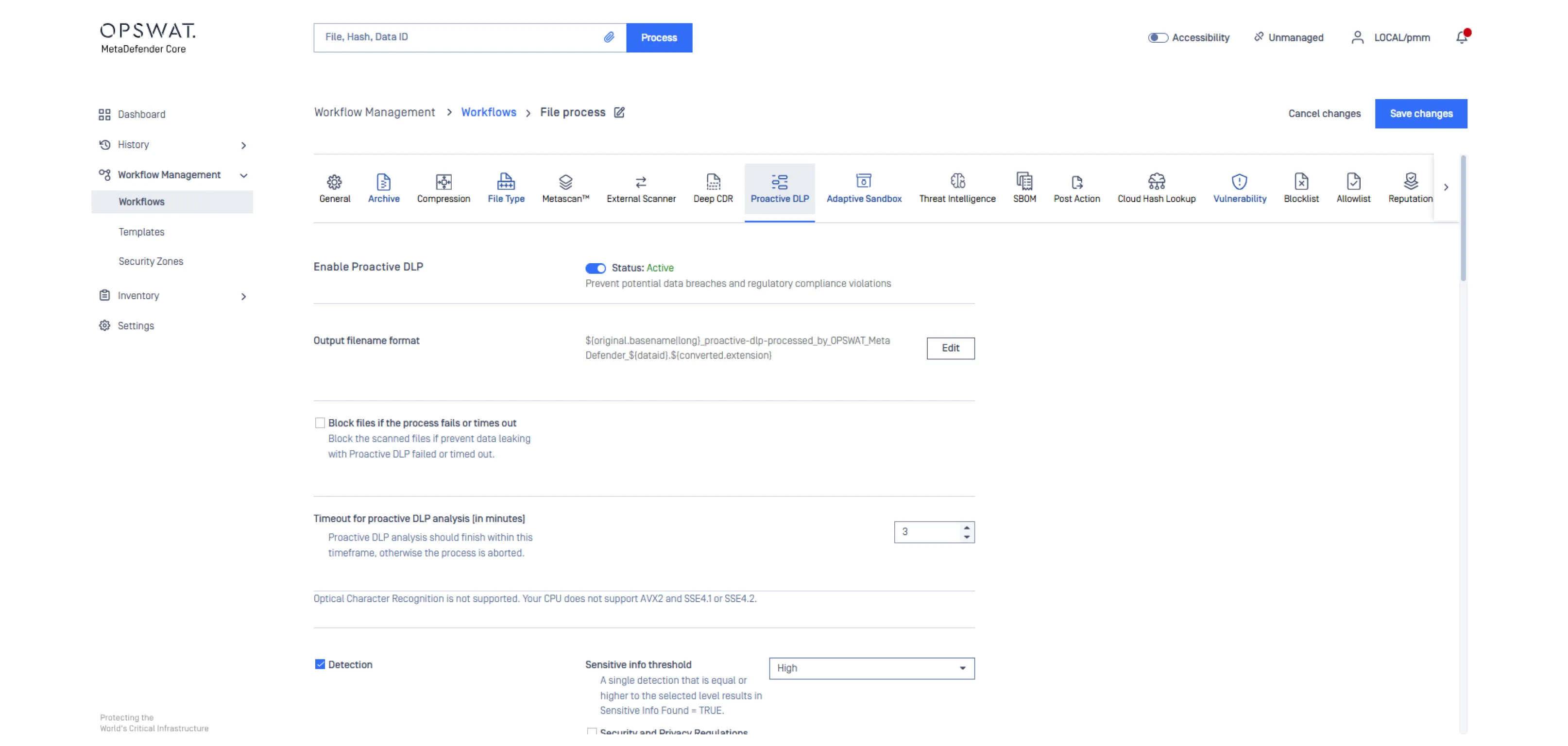
Define policies that identify and protect sensitive information through AI-powered data classification and pattern detection. Configure rules to address insider threat risks, monitor sensitive file movement, and enforce actions such as redaction, blocking, or alerting based on policy requirements.
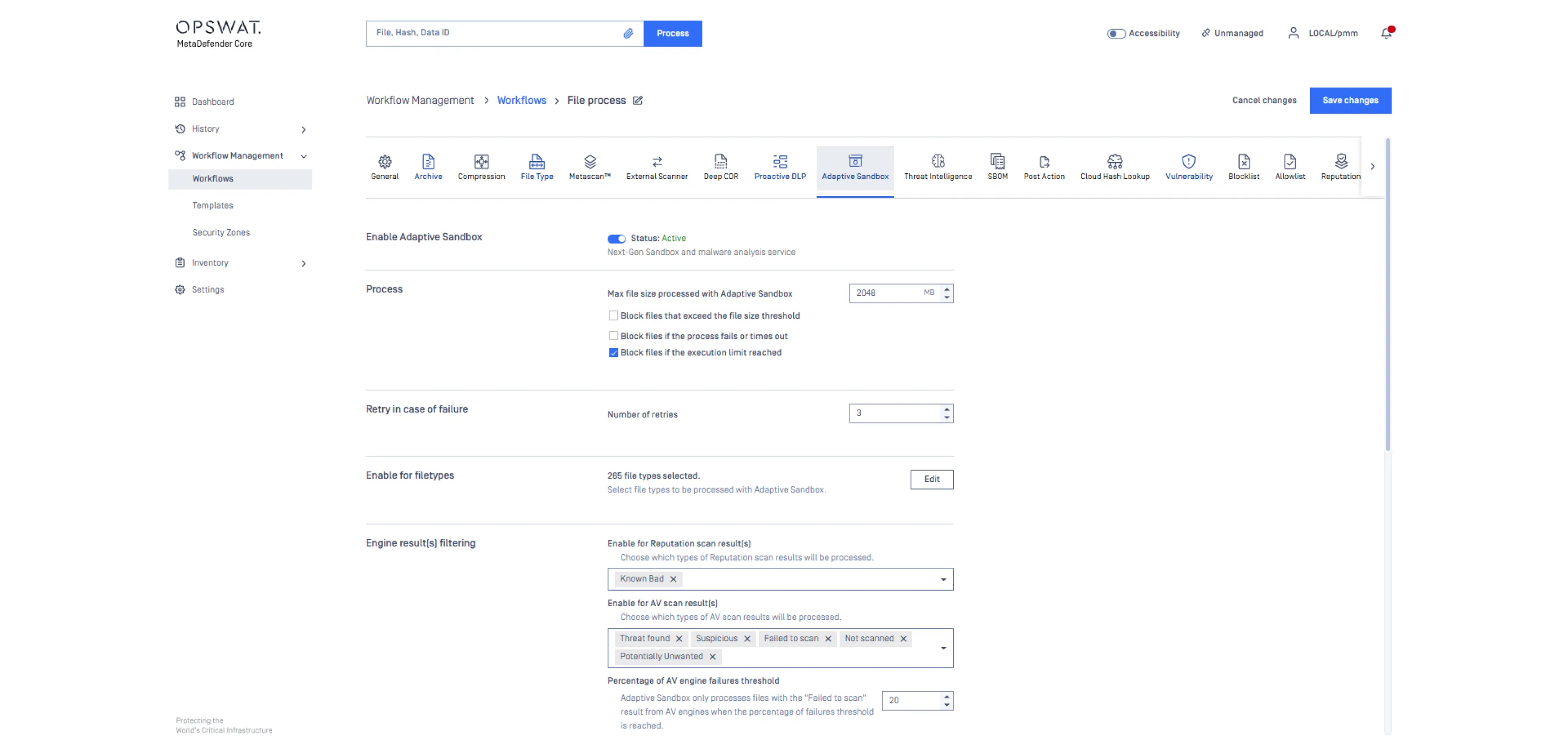
Enable emulation-based sandbox analysis for files that require deeper inspection. Configure how potentially unsafe content is executed in a controlled virtual environment, how behavior is evaluated, and how MetaDefender Core adjusts analysis depth based on file type, risk level, or workflow policy.
Enable emulation-based sandbox analysis for files that require deeper inspection. Configure how potentially unsafe content is executed in a controlled virtual environment, how behavior is evaluated, and how MetaDefender Core adjusts analysis depth based on file type, risk level, or workflow policy.
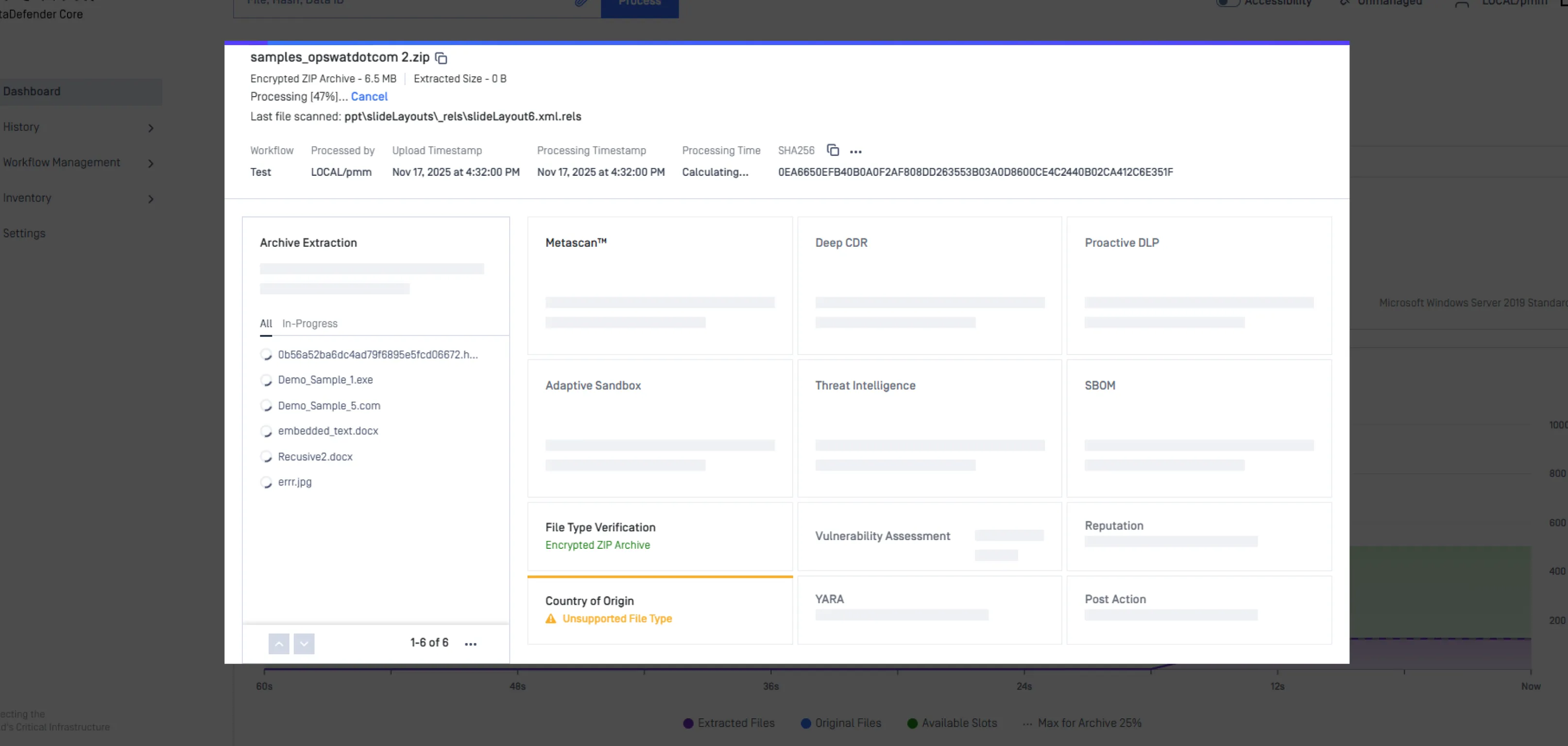
Files are going through different engines for malware and risk check. This process ensures that any potentially malicious content could not slip through the perimeter and reach end users.
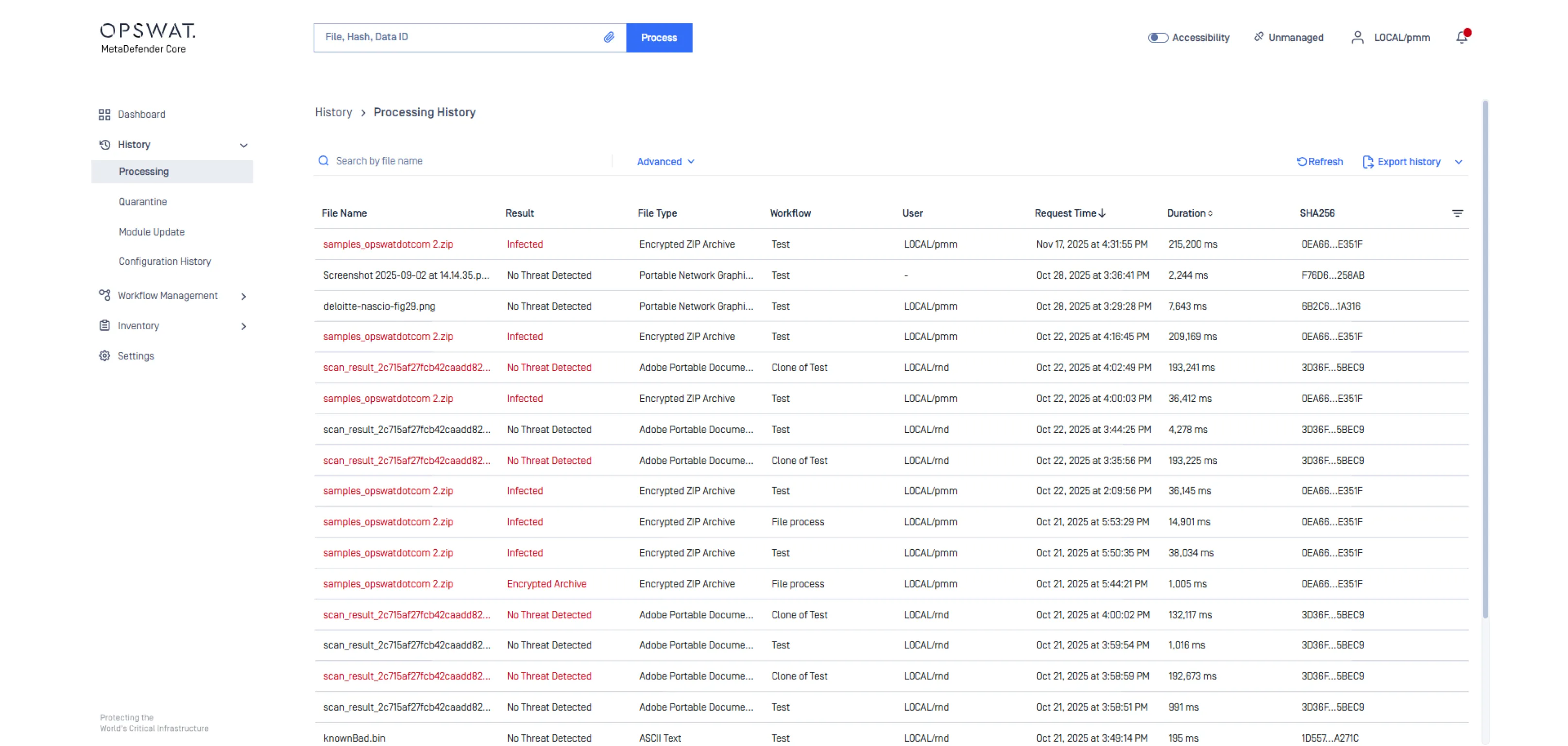
Review processed files, threats detected, policy actions, and system metrics. Generate reports for audits, compliance, and operational reviews.
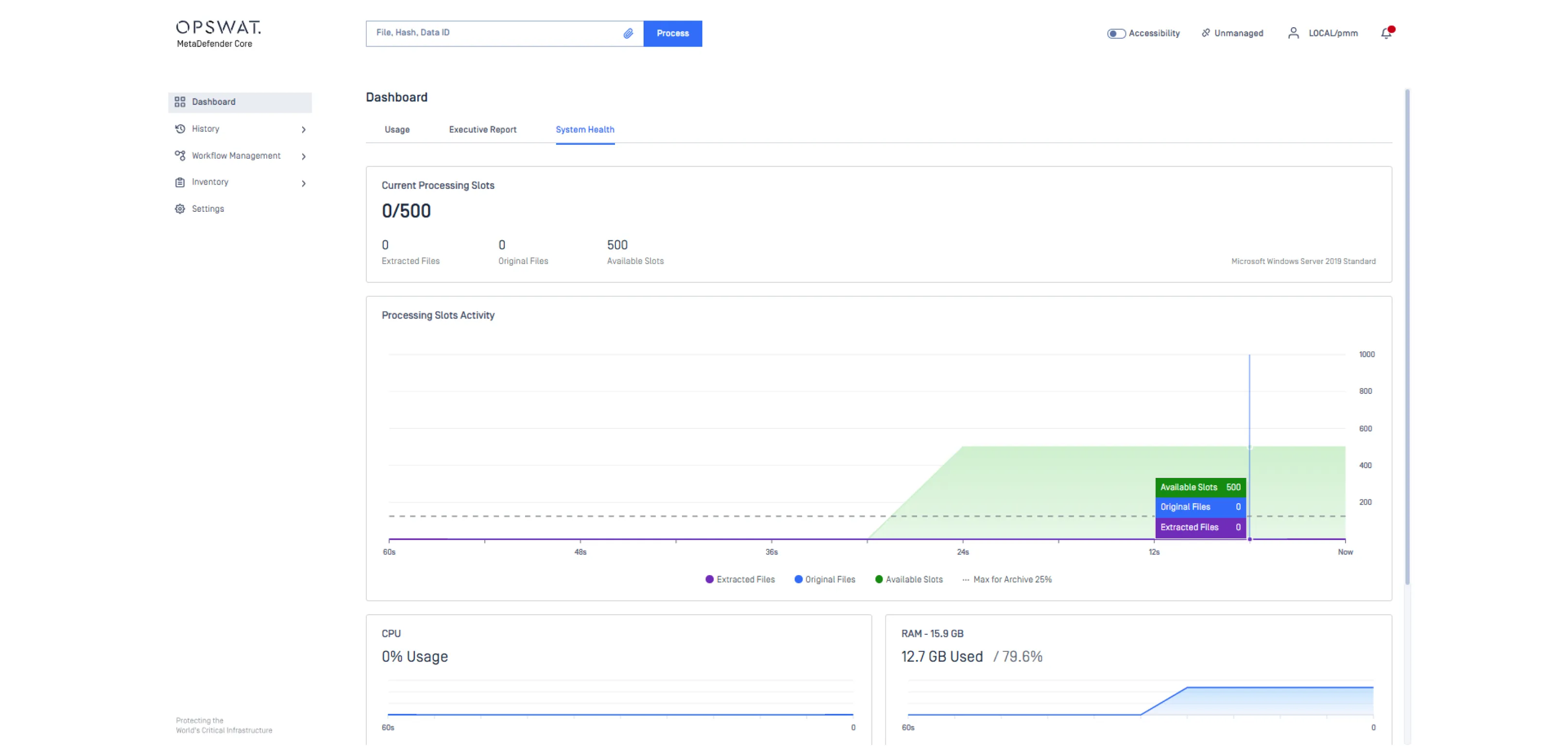
View a unified dashboard that summarizes processed files and threat activity. Access executive reports with detailed scan results. Monitor system availability and key resource metrics such as CPU, RAM, and engine status to maintain reliable performance.
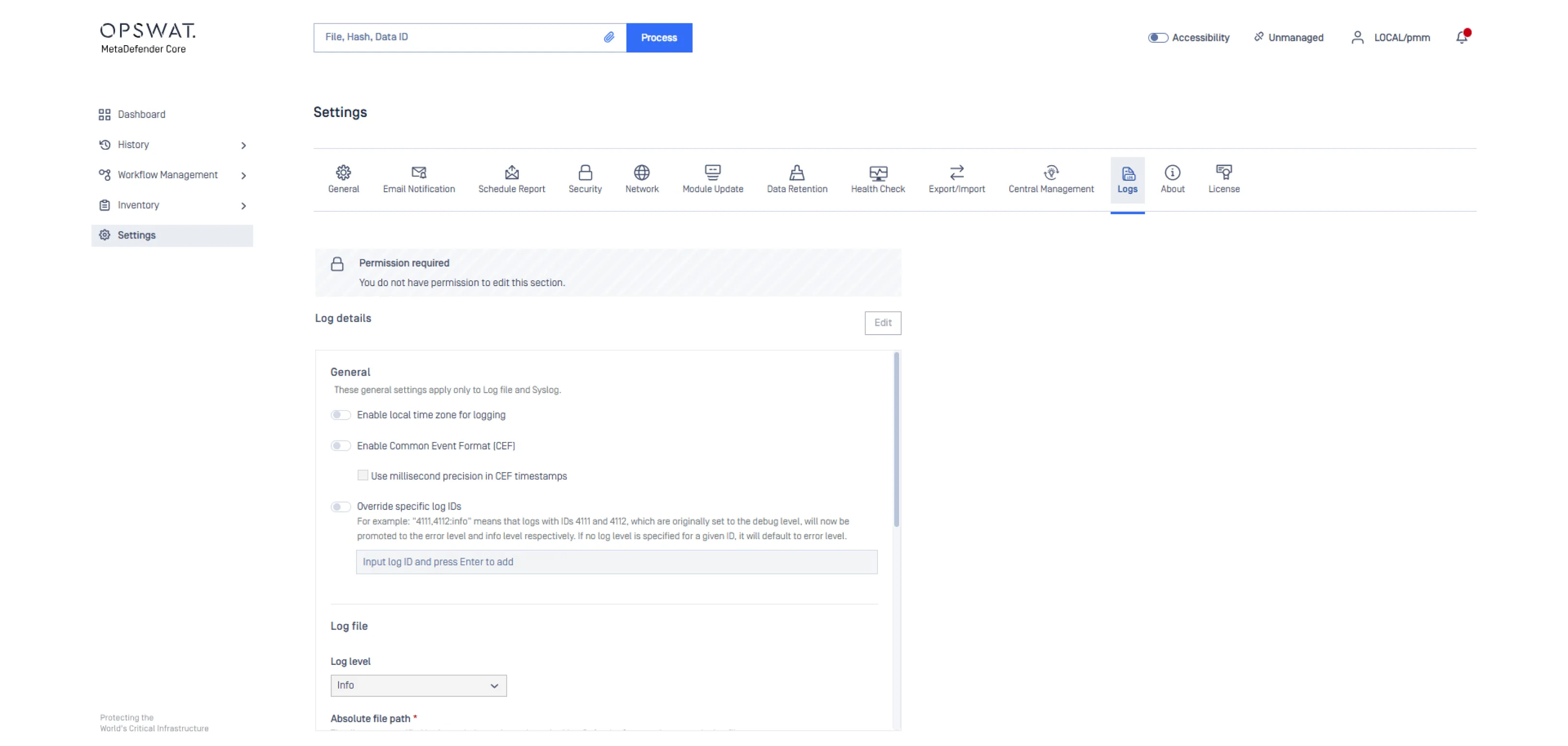
Connect MetaDefender Core to your infrastructure including SIEM, SOAR, ICAP servers, API workflows, and storage systems. Set logging and alerting preferences for automated responses.
AI-Enhanced Engines
100 % de protection
Verified by SE Labs for Deep CDR™ Technology

Confiance de la part de
2,000+
Organizations
Worldwide
99%+
Malware Detection Accuracy Across 30+ Anti-Malware Engines
200+ File Types and
30+ Archive Formats
#Leader n°1 du marché
Complete File Security With MetaDefender Core™
Sécurité du téléchargement de fichiers
MetaDefender Core protects public portals and applications from file-borne threats by sanitizing every uploaded file with Deep CDR™ Technology and scanning in parallel with 30+ anti-malware engines. It applies zero-trust principles at the perimeter, detects spoofed file types, and inspects encrypted archives to prevent ransomware and data leakage without disrupting the user experience.

File Download Security
MetaDefender Core ensures downloads are free from potential malware across browsers and secure web gateways by applying deep file sanitization and multi-engine malware scanning before execution. It blocks disguised or evasive threats that standard filters miss, maintains productivity, and provides full audit visibility for compliance and investigation.

Secure AI and ML Data Pipeline
MetaDefender Core secures AI data pipelines and workflows by sanitizing and validating every dataset, model, and dependency before use. It detects malware and vulnerabilities in ML artifacts, generates SBOMs for software transparency, and applies Proactive DLP to protect sensitive data, enabling trusted and compliant AI development and deployment.

Secure Forensics Investigation for SOC Teams

Deploy Anywhere. Secure Everywhere.
Designed for complex and regulated environments, MetaDefender Core adapts to your architecture and security needs while maintaining performance, resilience, and compliance.
Proven Protection for the World’s Most Secure Environments
Aid Compliance with Regulatory Requirements
Designed for regulated environments, MetaDefender Core enforces secure file handling and documentation practices aligned with major global standards. Boost your compliance posture without compromising business continuity.