Importation (Basse→Haute)
- Empêche les logiciels malveillants de pénétrer dans les réseaux classifiés.
- Combine Multiscanning,Sandbox Adaptive Sandbox , la technologie Deep CDR™, le contrôle unidirectionnel et les interruptions de protocole.
Les solutions OPSWAT constituent une solution de sécurité modulaire permettant de transférer des données en toute sécurité entre des réseaux présentant des niveaux de confiance et de classification différents. S'appuyant sur la MetaDefender , elles associent des fonctionnalités avancées de prévention des menaces, des diodes de données et des passerelles de sécurité afin d'appliquer des contrôles d'importation et d'exportation, de prévenir les logiciels malveillants et les fuites de données, et de prendre en charge des flux de travail conformes aux normes pour les environnements de défense, de renseignement et d'infrastructures critiques.


Les données qui circulent entre les domaines se présentent aujourd'hui sous des volumes importants et des formats divers, depuis les fichiers des utilisateurs quotidiens jusqu'aux données géospatiales, en passant par les programmes d'installation et les mises à jour d'applications. Les systèmes hérités et uniquement matériels peinent à traiter cette variété et ne peuvent pas s'adapter pour fournir les fonctions de renforcement de la sécurité (SEF) nécessaires d'une manière flexible et extensible.
Les systèmes doivent résister à des attaquants très ingénieux, y compris à des menaces émanant d'États-nations. Les transferts de données entre les niveaux de sécurité exposent des vulnérabilités que les défenses traditionnelles ne peuvent pas traiter, tandis que les attaques basées sur l'IA exigent une protection moderne et adaptative.

L'isolement permanent des données ne répond plus aux besoins de collaboration interterritoriale. Les systèmes CDS modernes doivent s'adapter aux exigences des entreprises, en prenant en charge divers volumes, types de données et applications, tout en permettant des transferts transparents d'APIAPI et de cloud à on-prem.
OPSWAT propose une approche modulaire et logicielle qui s'ajoute aux processus existants,
avec des technologies de pointe.
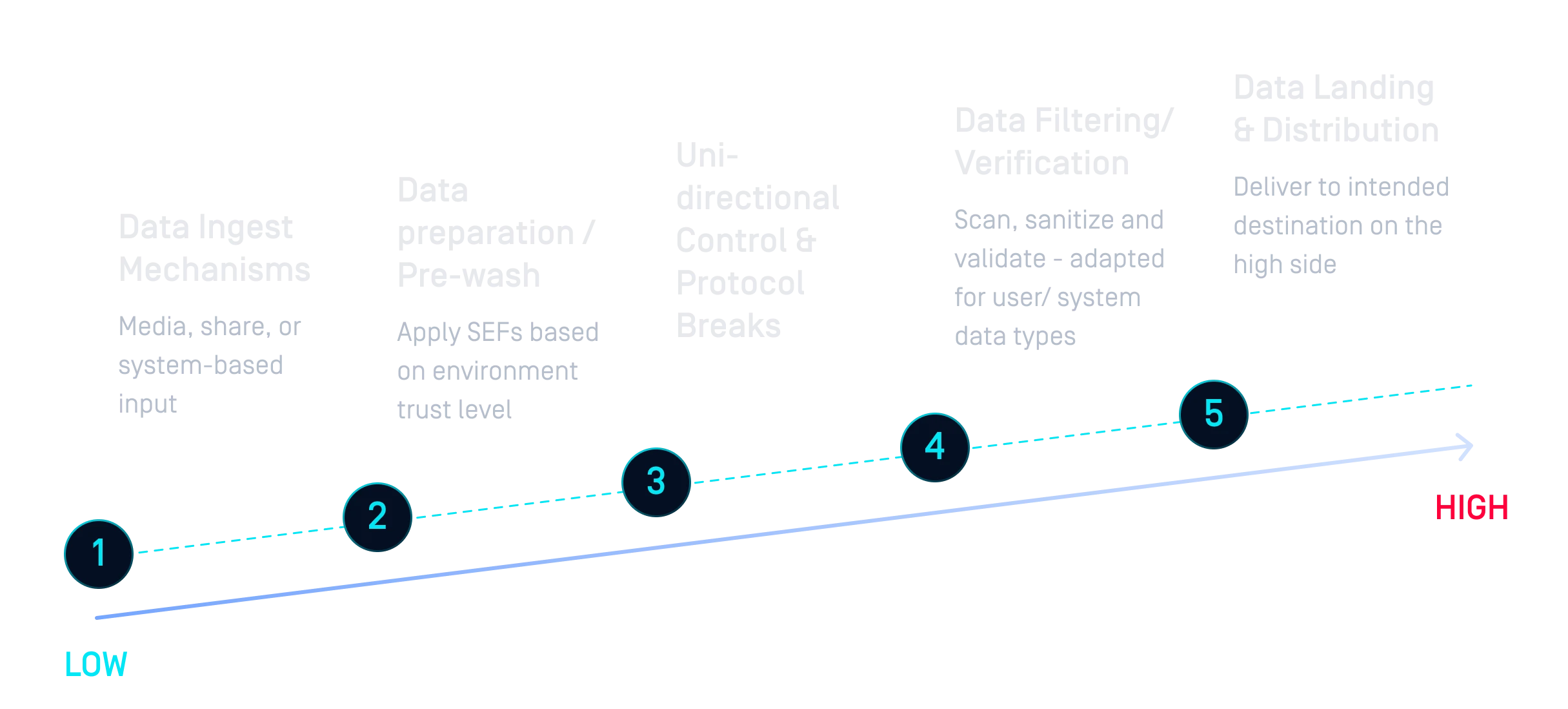
Avec des technologies leaders sur le marché et des capacités de connexion et de déconnexion, l'approche modulaire d'OPSWATest un moyen plus efficace de construire des solutions CDS.
Grâce au bac à sable d'émulation, les entreprises peuvent examiner les IOC dans des types de données complexes tels que les correctifs ou les applications du système d'exploitation et éliminer les vecteurs de menace potentiels.
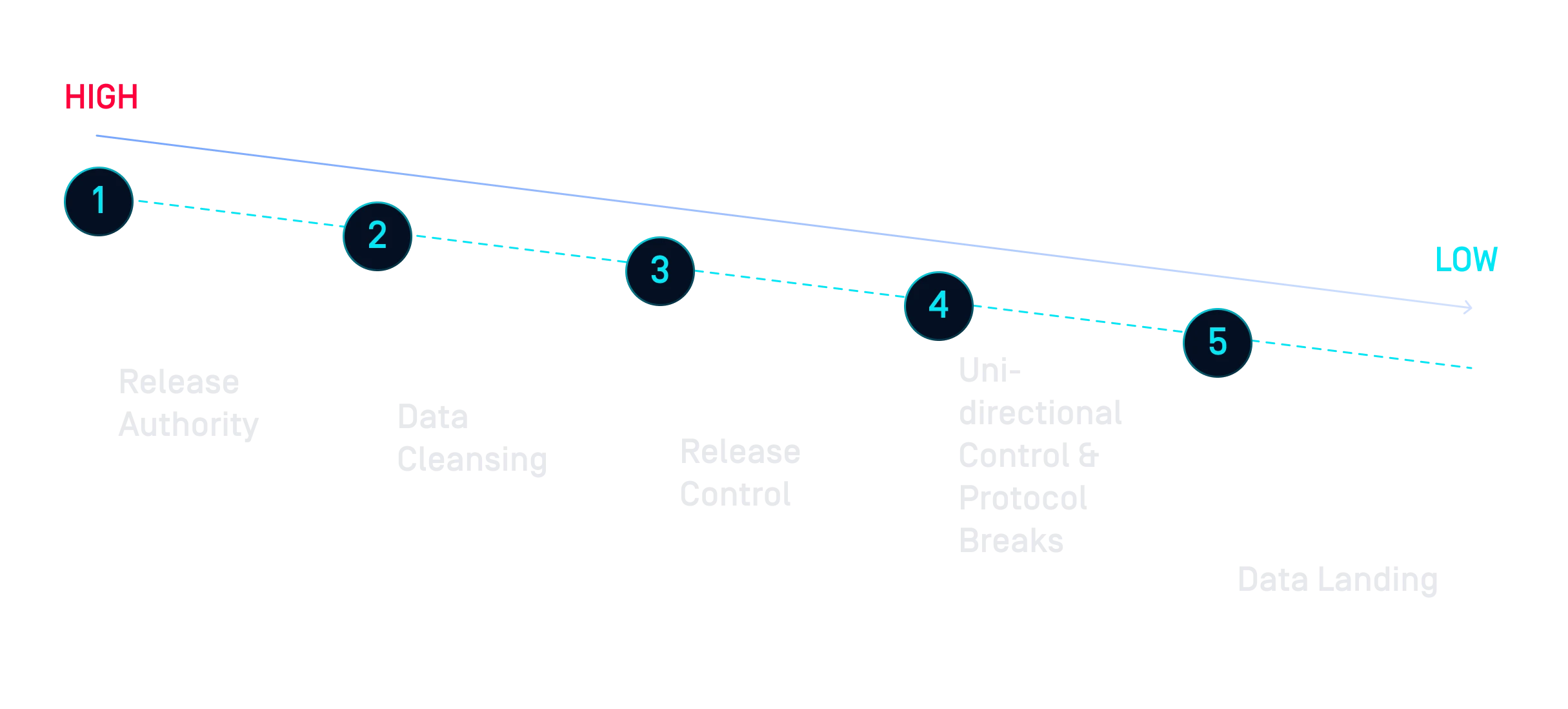
La Proactive DLP peut contribuer à garantir que les données transférées d'une classification supérieure à une classification inférieure (comme les rapports partagés avec des partenaires) ne contiennent pas d'informations sensibles qui ne sont pas destinées à être publiées, en les détectant et en les bloquant dans les fichiers.
Avec MetaDefender Kiosk, les données provenant de Media amovibles peuvent être soumises aux mécanismes de sécurité appropriés en fonction de la position de risque de votre organisation.
L'un des principaux avantages est que l'utilisation de MD Core en conjonction avec des outils tels que MFT permet une piste d'audit complète, ce qui permet aux organisations de remonter jusqu'au rôle ou à la personne qui a tenté d'exfiltrer les données.
Contrairement aux approches traditionnelles qui isolent les données et rendent la collaboration difficile, les solutions d'OPSWATs'intègrent dans des architectures interdomaines et appliquent des politiques de sécurité. L'approche hybride matériel-logiciel prend en charge de multiples communautés d'intérêt tout en garantissant que les données sensibles sont correctement contrôlées, surveillées et auditées.
Alors que les cyberattaques et les acteurs qui les mènent deviennent de plus en plus sophistiqués, les instances dirigeantes du monde entier mettent en place des réglementations pour s'assurer que les infrastructures critiques font le nécessaire pour rester sécurisées.