Les documents Microsoft Office restent l'un des outils les plus efficaces pour les cyberintrusions. Ils sont fiables, largement utilisés et profondément ancrés dans les opérations quotidiennes. Les activités récentes liées à des acteurs malveillants russes, combinées à des vulnérabilités telles que CVE-2026-21509, montrent pourquoi Office continue d'être un point d'entrée fiable, en particulier contre les environnements sensibles et de grande valeur.
La vulnérabilité : exploiter la confiance par conception
CVE-2026-21509 permettait aux pirates informatiques de transformer un document Office légitime en arme, de sorte que l'exploitation se produisait lors du traitement normal du fichier. Pas de macros. Pas d'avertissements. Pas de signaux d'alerte évidents. Le document semblait ordinaire car, structurellement, il l'était.
C'est là le problème. Les fichiers Office sont des conteneurs complexes. Ils prennent en charge des objets intégrés, des références et du contenu dynamique conçus pour améliorer la productivité. Cette même complexité permet aux pirates informatiques de dissimuler des chemins d'exécution dans le traitement normal des documents.
Comment fonctionne l'exploit
Microsoft Office comprend un gestionnaire de sécurité qui agit comme un gardien pour les objets intégrés. Lorsque Office rencontre un objet OLE, il vérifie une liste de blocage (Kill Bits) afin de déterminer si cet objet est dangereux.
CVE-2026-21509 exploite directement ce mécanisme de confiance. Les pirates intègrent des propriétés et des indicateurs spécifiques dans la structure XML du document. Ces indicateurs présentent essentiellement des informations d'identification au gestionnaire de sécurité, signalant « cet objet est fiable, ne le vérifiez pas ». Le gestionnaire de sécurité se conforme à cette demande et l'objet OLEmalveillant s'exécute sans contrôle.
L'exploitation se produit tôt, pendant l'analyse et le rendu. Le document n'a pas besoin d'avoir l'air malveillant. Il suffit simplement qu'il soit ouvert.
Une tendance, pas une exception
CVE-2026-21509 suit un schéma familier.
Dans CVE-2024-30103, les attaquants ont exploité la manière dont Office traitait les modèles distants, permettant ainsi l'exécution sans macros et avec une interaction minimale de l'utilisateur. Auparavant, CVE-2023-36884 était activement exploité par des groupes liés à des États via des documents Office spécialement conçus qui se déclenchaient lors du rendu normal.
Chaque cas renforce le même point : l'exploitation se produit tôt, pendant l'analyse et le rendu. Le document n'a pas besoin d'avoir l'air malveillant. Il suffit simplement qu'il soit ouvert.
Cette approche correspond bien au mode opératoire des groupes malveillants russes. Ceux-ci privilégient les techniques qui s'intègrent dans les flux de travail normaux, évitent les indicateurs bruyants et exploitent la confiance plutôt que de forcer l'accès.
La véritable leçon à tirer des premiers jours au bureau
La leçon ne porte pas sur une vulnérabilité ou une campagne en particulier. Elle porte sur la surface d'attaque elle-même.
Les documents Office sont généralement traités comme des données, et non comme du contenu exécutable. Les exploits modernes tirent parti de cette hypothèse. Les équipes de sécurité ne peuvent pas se fier à leur connaissance des vulnérabilités actives ou des exploits en circulation à un moment donné. Les zero days fonctionnent précisément parce qu'ils sont inconnus lorsqu'ils sont utilisés.
Pour les organisations qui exploitent des systèmes critiques, cela change la donne en matière de sécurité. L'accent ne peut plus être mis sur l'identification de l'exploit après l'ouverture d'un document. Il faut désormais s'attacher à supprimer toute possibilité pour les documents d'exécuter une logique cachée.
Comment OPSWAT répond à cette menace
OPSWAT le défi des vulnérabilités zero-day dans Office grâce à deux technologies complémentaires : la technologie Deep CDR™ empêche l'exploitation en supprimant la capacité d'exécution, tandis que Adaptive Sandbox les véritables intentions des documents malveillants grâce à une analyse comportementale.
Technologie Deep CDR™ : neutralisation des exploits grâce à l'assainissement structurel
La technologie Deep CDR™s'attaque au problème à la source en adoptant une approche « zero trust » (confiance zéro) vis-à-vis de la structure des fichiers.
Au lieu de déterminer si un document est malveillant, la technologie Deep CDR™ traite par défaut les fichiers complexes comme potentiellement dangereux. Elle décompose le document, supprime tous les éléments actifs et exploitables (scripts, objets intégrés, structures malformées) et reconstruit une version propre qui préserve le contenu professionnel.
Comment la technologie Deep CDR™ bloque CVE-2026-21509
La technologie Deep CDR™ fonctionne selon un principe fondamentalement différent de celui d'Office Security Manager. Elle n'évalue pas la fiabilité. Elle ne vérifie pas les listes noires et n'analyse pas les indicateurs. Elle supprime simplement tout contenu non conforme à la politique, y compris les objets OLE.
En déconstruisant le document et en éliminant tous les éléments actifs et exploitables avant sa reconstruction, la technologie Deep CDR™ rend le mécanisme d'exploitation inerte. Il ne reste aucun OLEObject à exécuter, qu'il soit fiable ou non. Le document qui en résulte conserve son contenu professionnel, mais ne peut plus être exécuté.
Cette approche ne nécessite aucune connaissance de CVE-2026-21509 ou de toute variante future. Si l'exploitation dépend de la survie d'objets intégrés dans l'environnement utilisateur, elle échoue par conception.
Pour les RSSI, cela redéfinit le débat sur les risques. Les vulnérabilités zero-day dans Office ne sont plus un problème de renseignement, mais deviennent un choix de conception. Le document peut arriver, mais il arrive sans la capacité d'exécuter une logique cachée.
SandboxAdaptive : détecter les intentions malveillantes grâce à l'analyse comportementale
Alors que la technologie Deep CDR™ empêche l'exploitation grâce à la désinfection structurelle, Adaptive Sandbox adopte une approche différente : elle exécute le document dans un environnement contrôlé et observe ce qu'il fait réellement.
Pourquoi l'analyse comportementale est importante
CVE-2026-21509 démontre pourquoi l'analyse statique a ses limites. Les documents malveillants associés à la campagne APT28 en Ukraine semblent normaux d'un point de vue structurel. Les indicateurs intégrés dans le XML ne sont pas enregistrés comme des signatures malveillantes évidentes. Les méthodes de détection traditionnelles ont du mal à fonctionner, car il n'y a rien de manifestement « anormal » à détecter.
Adaptive Sandbox différemment. Plutôt que d'essayer d'identifier des modèles malveillants dans un code statique, il exécute le document dans un environnement contrôlé et observe son comportement réel.
Comment Adaptive Sandbox la campagne APT28
Lorsque Adaptive Sandbox les documents malveillants exploitant CVE-2026-21509, il n'a pas recherché de signatures d'exploits connues. Il a exécuté le document et observé ce qui se passait.
Documents malveillants réels exploitant CVE-2026-21509
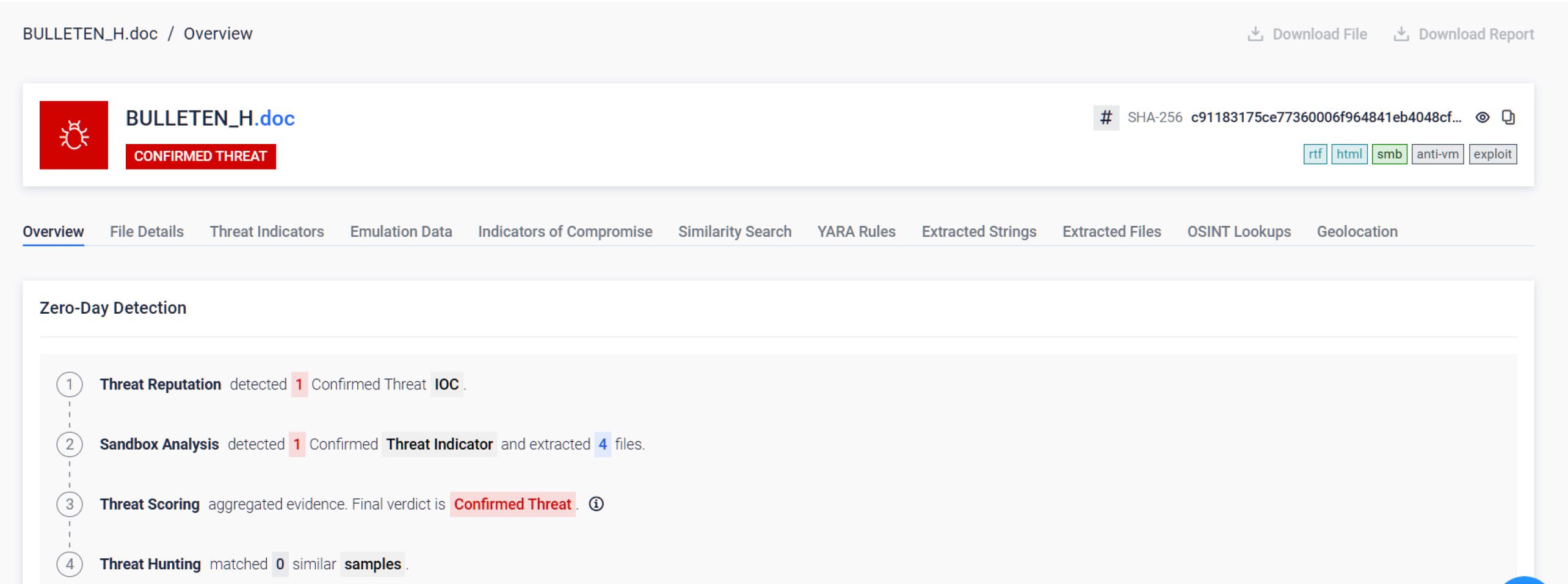
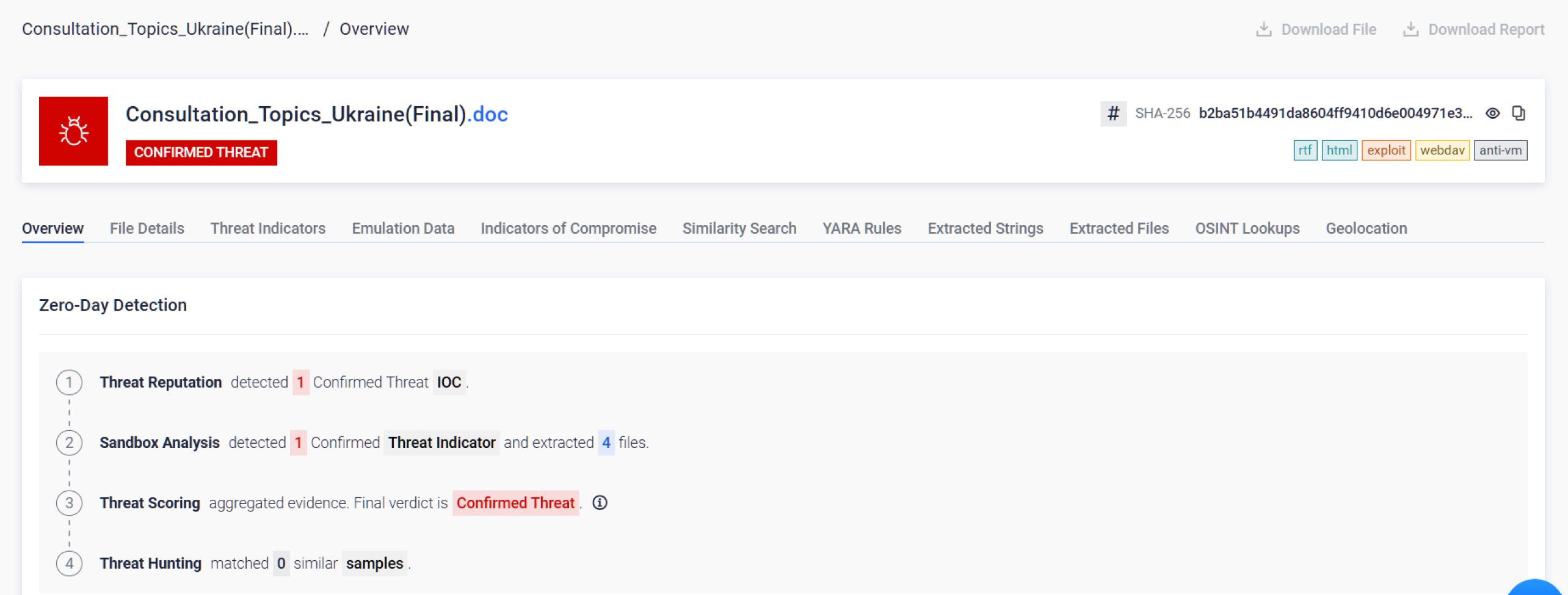
Dès l'ouverture du fichier, l'objet OLEObject intégré s'est déclenché, exactement comme le souhaitait le pirate. Mais au lieu d'atteindre le réseau de la victime, il a révélé son véritable objectif : établir une connexion WebDAV vers l'infrastructure d'un acteur malveillant externe afin de récupérer la charge utile de la phase suivante.
C'est le comportement du réseau qui importe. Pas la structure XML. Pas la présence d'indicateurs spécifiques. L'action réelle que le document effectue lorsqu'il a la possibilité de s'exécuter.
Adaptive Sandbox et émule tous les éléments actifs et exploitables, créant ainsi un profil comportemental complet. Même si une exploitation est inconnue, si un document tente d'accéder à des serveurs externes, de télécharger des charges utiles supplémentaires, d'exécuter des commandes cachées ou d'établir des connexions de commande et de contrôle, Adaptive Sandbox ce comportement avant que le document n'atteigne les utilisateurs.
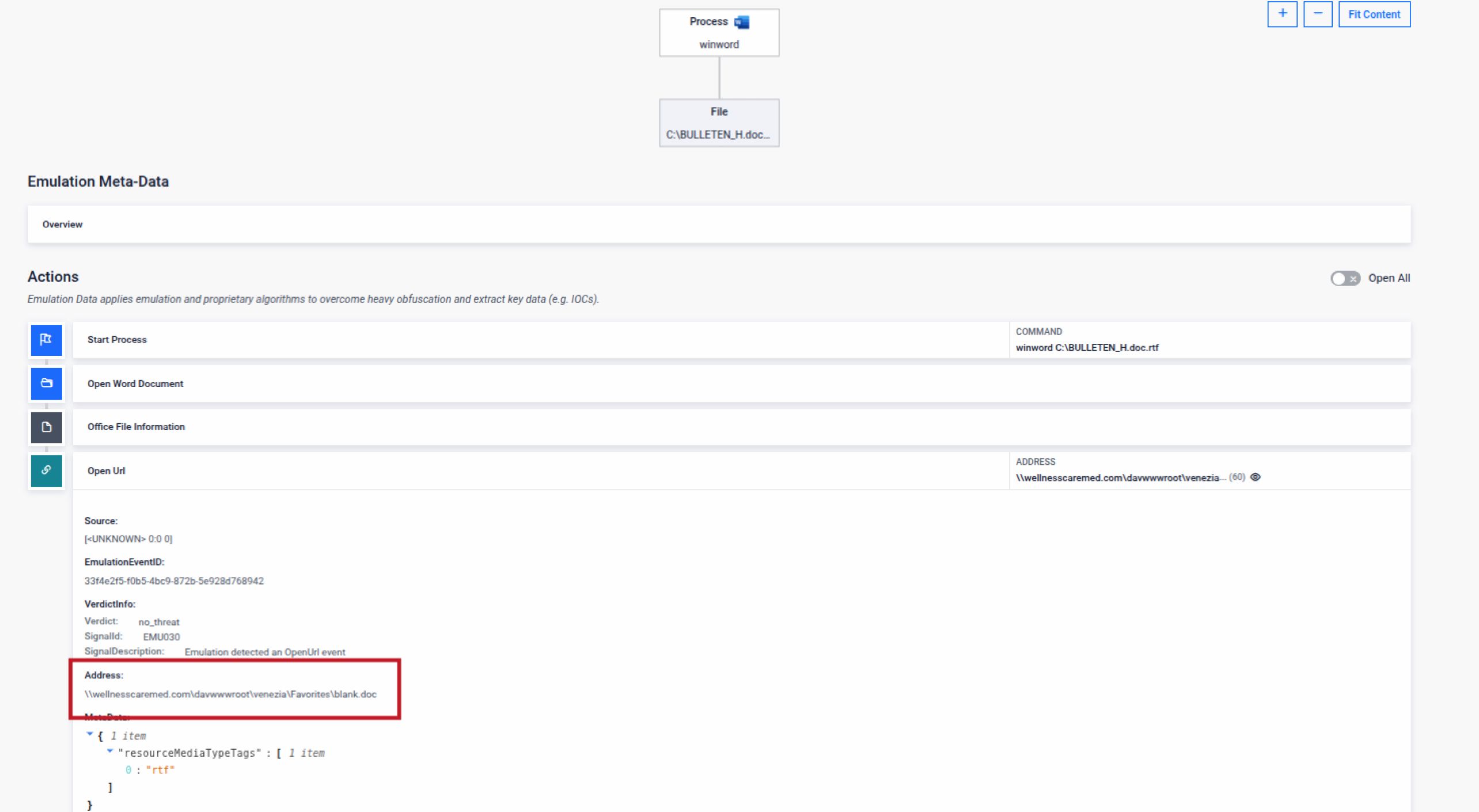
Si l'OLEObject contient du code malveillant, Adaptive Sandbox leSandbox grâce à l'exécution comportementale, et non à la correspondance de signature.
Deux technologies qui fonctionnent ensemble
Pour les organisations opérant dans des environnements à haut risque, la technologie Deep CDR™ et Adaptive Sandbox des rôles distincts mais complémentaires :
- Technologie Deep CDR™ pour la prévention : garantit que les documents entrant dans l'environnement ne peuvent pas exécuter de logique malveillante. La capacité d'exploitation est supprimée avant que le fichier n'atteigne les utilisateurs. Utilisez cette technologie lorsque les documents doivent être nettoyés pour être transmis en toute sécurité aux utilisateurs finaux.
- Sandbox Adaptive Sandbox la détection : révèle l'intention comportementale des documents suspects grâce à une exécution contrôlée, en prenant en charge les renseignements sur les menaces, la réponse aux incidents et l'analyse forensic. Utilisez cette fonctionnalité lorsque vous avez besoin de comprendre exactement à quoi sert un document.
CVE-2026-21509 exploite la confiance dans la structure des fichiers. La technologie Deep CDR™ supprime la structure exploitable. Adaptive Sandbox ce que l'exploit était censé faire.
Aucune de ces deux approches ne nécessite de connaître la vulnérabilité à l'avance. Elles garantissent toutes deux que lorsque la prochaine faille zero day Office apparaîtra, votre organisation n'aura pas à attendre pour découvrir ses effets.
Conclusion : la sécurité dès la conception, et non la détection
Les exploits Office continueront d'apparaître. Les acteurs malveillants continueront d'exploiter la complexité des fichiers, car cela fonctionne. La conclusion pratique est simple : dans les environnements à haut risque, les documents Office doivent être sécurisés dès leur création. Ils ne doivent pas être surveillés ni considérés comme « probablement sains ». Ils doivent pouvoir être ouverts en toute sécurité.
CVE-2026-21509 ne sera pas la dernière faille Office exploitée par les pirates russes. La prochaine existe peut-être déjà. La seule question pertinente est de savoir si les documents ont la possibilité d'exécuter une logique cachée dans votre environnement.
Découvrez comment intégrerSandbox la technologie Deep CDR™ et Adaptive Sandbox à votre infrastructure de sécurité existante.

